November 03, 2022
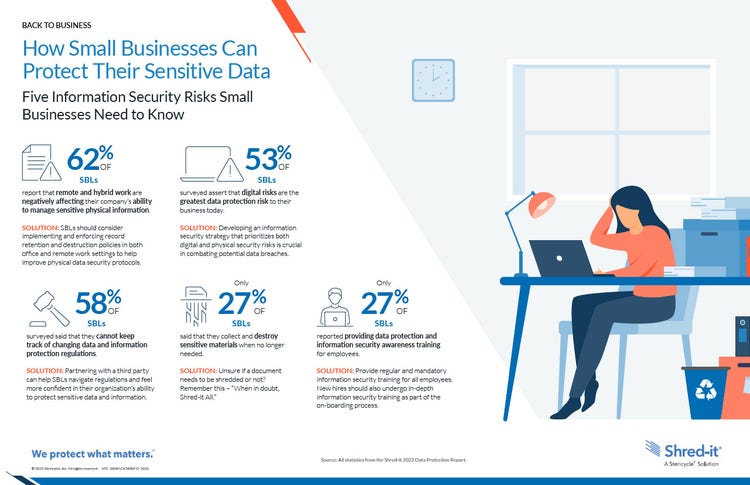
Five Information Security Risks Small Businesses Need to Know
IBM reports that the global average total cost of a data breach in 2022 is $4.35 million USD (about $5.5 million CAD), 2.6% increase from last year. For most companies, it’s not a question of if a data breach will occur, but when.
While larger businesses may have more resources in the form of tools, training, and staff, small businesses may struggle to understand and comply with the changing regulatory landscape. According to the 2022 Shred-it Data Protection Report (DPR), 58% of small business leaders (SBLs) said that they cannot keep track of shifting privacy regulations, and about 25% of SBLs do not understand the laws and how to comply with the rules that apply to them.
According to the 2022 DPR, SBLs surveyed know that data security is a necessary foundational element in building and retaining strong relationships with their customers, employees, and partners. More than 90% of SBLs believe that physical and digital data protection are equally important. However, many SBLs (53%) assert that digital risks are the greatest data protection risk to their business today, and only 27% say they collect and destroy sensitive materials when no longer needed.
Can your Small Business Afford a Data Breach?
Small businesses were already at higher risk for a data breach than larger companies, but the risk has drastically increased over the last few years. According to Tripwire, between 2020 and 2021, data breaches at small businesses globally soared 152% in comparison to the previous two years.
The severe financial loss and potential reputational harm caused by a breach are overwhelming for any sized organization, but especially for small businesses that may not have the resources to recover. Over 60% go out of business within six months of falling victim to a data breach.
Small business owners should be aware of the risks of a data breach and make data security a priority.
In this infographic, you will learn:
- The policies and procedures to have in place to help prevent a security breach
- The importance of training employees on information security protocols
Solutions for protecting sensitive data and what Shred-itTM can do for you as a trusted third-party organization